Lock object in SAP ABAP is used to prevent multiple users from making changes to the same piece of data simultaneously. A lock is a mechanism that prevents a user from modifying a record that is already being accessed by another user.
A lock object in SAP is defined using the Lock Object Administration t-code SM12 and is used to control access to specific data records. When a user tries to access a locked record, SAP will either block the access or provide a message indicating that the record is already locked.
The lock object in SAP is based on a locking mechanism known as enqueuing. When a user creates a lock, the lock object creates an entry in the lock table with the name of the object being locked, the user ID of the user who created the lock, and the type of lock. When another user tries to access the locked object, SAP will check the lock table to see if a lock exists for that object. If a lock exists, the user will either be blocked or given a message indicating that the object is already locked.
Types of Lock Object
There are two types of lock objects are available, DEQUEE, ENQUEE:
-
ENQUEUE: This is the mode that is used to lock an object. When a lock is created, an entry is made in the lock table, which prevents other users from accessing the locked object until the lock is released.
-
DEQUEUE: This is the mode that is used to release a lock. When a user releases a lock, the entry is removed from the lock table, and other users can then access the object.
Both the ENQUEUE and DEQUEUE modes are required for lock objects to function properly. The ENQUEUE mode is used to create the lock, and the DEQUEUE mode is used to release the lock. If a user creates a lock and does not release it, the object will remain locked indefinitely, preventing other users from accessing it.
Lock Mechanism
The lock mechanism in SAP allows programs to prevent conflicts when accessing the same data record. There are two main functions accomplished with the lock mechanism:
-
Communication: A program can communicate with other programs about data records that it is reading or changing. By locking the data record, the program signals to other programs that it is currently accessing the data and prevents them from accessing it until the lock is released.
-
Prevention: A program can prevent itself from reading data that has just been changed by another program. By requesting a lock on the data record, the program ensures that it has exclusive access to the data until the lock is released. This prevents any other programs from modifying the data and ensures that the program is working with the most up-to-date version of the data.
To request a lock, a program generates a lock request, which is sent to the Enqueue server. The Enqueue server creates a lock entry in the lock table and sets the lock, allowing the program to access the data. Once the program has finished accessing the data, it releases the lock, and the lock entry is removed from the lock table, allowing other programs to access the data.
Locking Mode
In SAP, there are severl locking modes available to control data access by multiple users. The most commonly used locking modes are:
- Exclusive Lock: The locked data can be read or processed by one user only.
- Shared Lock: Several users can read the same data at the same time, but as soon as a user edits the data, a second user can no longer access this data.
- Exclusive but not cumulative lock: Exclusive locks can be requested by the same transaction more than once and handled successively, but an exclusive but the not cumulative lock can only be requested once by a given transaction. All other lock requests are rejected.
- Update Lock: This mode is used when a user needs to modify a data record, but only after verifying that no other user has modified the data since it was last read. It allows the user to exclusively access the data record for the purpose of verifying that the data has not been modified by any other user, but does not prevent other users from reading the data.
- Intent Lock: This mode is used to indicate the intention of a user to lock a data record. It allows the user to signal to other users that it intends to modify the data, preventing them from acquiring an incompatible lock.
Advantages of Lock Objects in SAP
Lock objects in SAP offer several advantages, including:
- Data Consistency: Lock objects help maintain data consistency by preventing multiple users from simultaneously making changes to the same piece of data. This helps to avoid conflicting changes and ensures that all users are working with the most up-to-date version of the data.
- Data Integrity: By preventing multiple users from modifying the same data record simultaneously, lock objects help maintain data integrity. This ensures that the data remains accurate and complete.
- Improved Performance: Lock objects can help improve system performance by reducing the number of conflicts that can occur when multiple users try to access the same data simultaneously. This can help prevent system slowdowns and improve overall system performance.
- Reduced Errors: Lock objects can help reduce errors by preventing multiple users from making changes to the same data simultaneously. This helps to ensure that all changes are properly recorded and that there are no data conflicts or other errors.
- User Control: Lock objects provide users with greater control over their data by allowing them to lock data records that they are working on. This helps prevent other users from accidentally making changes to the same data and ensures that the user has exclusive access to the data until they release the lock.
How to Create Lock Objects?
Please follow the steps below to create a lock object:
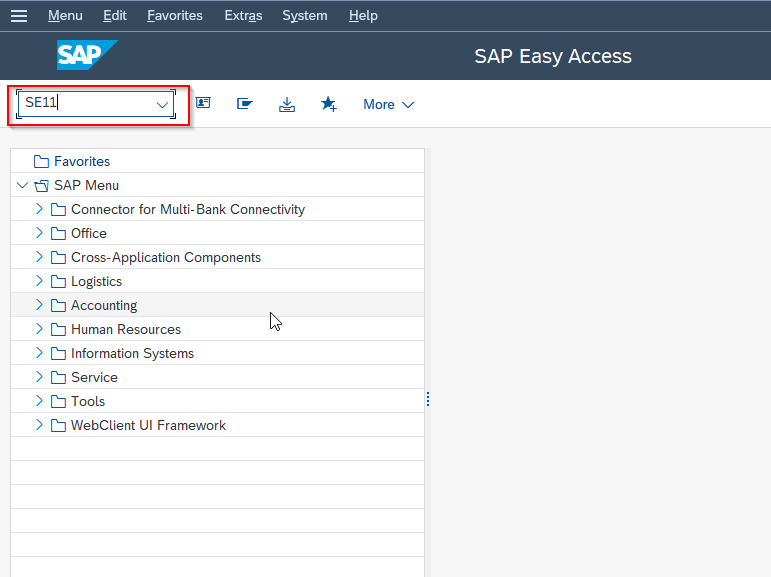
Enter t-code SE11 in the SAP command field and execute it
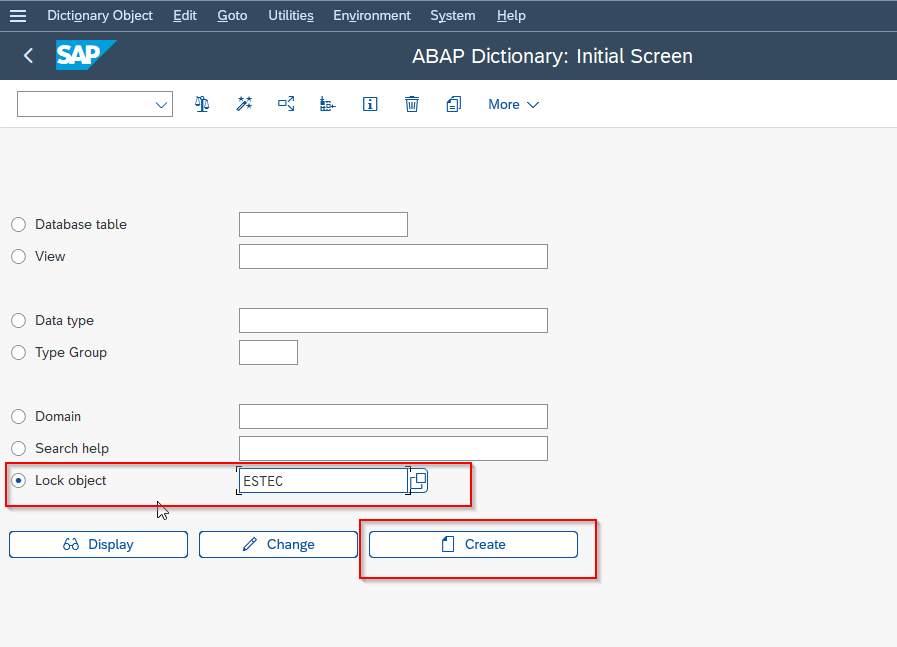
Next, click the Lock Object radio button. Enter the name of the lock object starting with E and click the Create button.
Enter the Short description field about the new lock object